Re-Post : How I managed to gain access to The Indian Digital treasure – 3 Billion documents on Digilocker
Hi Guys,
This is a repost of the blog that was written on https://yetanothersec.com/blog/2020/06/03/digilocker-disclosure/ as the yas portal is facing technical issues everynow and then. Also apologies for the bad quality of screen shots, i will find old files and update it later.
During the beginning of May 2020, there was a large commotion about the arogyasetu app and its security after a so called “hack” by infamous political hacker named Elliot Alderson. In light of all this, we at the YAS (Yet Another Security) community, had some talks in our WhatsApp group. So, it turned out to be a discussion on techniques used for bypassing SSL pinning on the mobile apps. This whole discussion made be curious about other apps from India government and since I have worked on similar projects outside of India, digilocker caught my attention.
Hence, I downloaded the app and installed on my test devices and fired up my favorite toolset burpsuite + Frida. I used my homebrewed pinning bypass scripts to actively intercept the app’s communication with the backend. To my surprise, I found that digilocker was not matching with the basic security features of arogyasetu, such as custom root detection, custom ssl pinning checks all wrapped inside obfuscated binary.
That made it interesting, I decided to dig in, as I was not current user of the platform it asked me to signup first and setup a pin to access the system. The immediate thing that caught my eye on the request to set pin was it was a normal http request with no session, in layman’s terms, the platform allows an anonymous user to set pin for any active user of the platform. Shocking!!!
To give more technical context, internally the system denotes each user with a unique v5 UUID (v5 denotes it has enough entropy and that there is less chance of duplication and has enough randomness to it), so to set a new pin for the user all you need is to call the endpoint with uuid and new pin value.
All of this made me think about how to bypass sms otp of a user, because pin is asked after the OTP. So by looking at how the communication progresses between mobile app and backend server I came to conclusion that the steps of verifying sms otp and submitting pin are not linked together. Meaning you can do the sms otp as one user and submit pin of second user and finally you will end up logging in as second user. Bingo!!!
I figured all this by looking at the mobile app of digilocker, wait a minute there is a web portal for digilocker. I started to look at the web portal of digilocker, this then gave me more internal knowledge on the mobile app. Here are some observations that I sent to CERT-IN and digilocker teams.
Timelines
May 10th – I reported this to CERT-IN
May 14th – CERT-IN finally acknowledged the issue
May 28th – CERT-IN confirmed the issues are fixed
June 3rd – I saw another blog with similar findings and decided to write one of my own.
Credits
Dedicated to all 215 members who are my hardcore brothers & sisters from YAS community. Thanks for all your support and inspiration to do this.
Detailed observations
Below is a summary of the findings that i found, I just gave risk rating based on industry standards for each.
1) OTP bypass due to lack of authorization – Critical
The OTP function lacks authorization which makes it possible to perform OTP validation with submitting any valid users details and then manipulation flow to sign in as totally different user. Let’s assume attacker creates/gets hold of a valid dummy account.
Attack path
- Use any valid account attacker has access to and complete otp
- Proceed with pin submission to totally different victim account
- Logs into victim account
Below is attack steps
- Attacker uses a valid user account that he has access and starts the login process by submitting phone number.
- The submission of otp via both mobile and web app is on url https://accounts.digitallocker.gov.in/signin/verify_otp
- Attacker completes the OTP validation with account (mobile number) he possesses.
- Attacker proceeds to submit the secret pin
- Mobile calls two urls for this – POST request
- Web application calls two urls – POST request
- All the above calls posts a base64 combination of user_uuid:secret_pin (similar to basic auth) on the parameter loginTxn
- Attacker modifies these calls to call any users uuid and secret pin combo before it is submitted
- Attacker logs in as victim now, hence the victims otp protection is bypassed
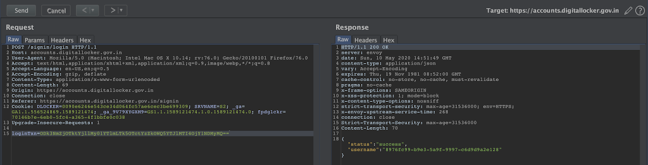
Sample screen shot of login call, similar calls can be observed to all above mentioned urls.
2) Secret PIN Bypass/takeover – Critical
The pin setting API/URL lacks any authorization and can be used to reset pin of any user without authentication.
Attack path
- Attacker finds the uuid of a user or randomly picks one
- Attacker sets the pin via the url
- Attacker uses vulnerability #1 mentioned above to gain access to the account
Below is attack steps
- Attacker submits the uuid of the user and new pin to the url https://accounts.digitallocker.gov.in/signup/set_pin
- Pin gets updated
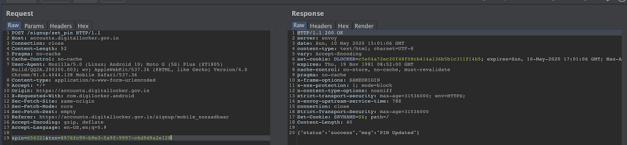
Sample screenshot of the call. Notice there is no session related information on the POST request so its not bound to any user
3) Poor session mechanism in APIs – High
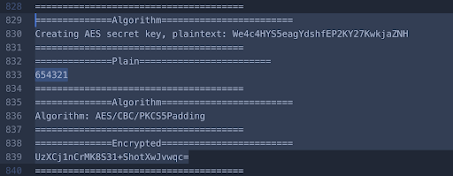
It was observed that the API calls from mobile were using basic authentication to fetch data or do transactions. All calls from mobile has a header flag is_encrypted: 1 which denotes that the user has to submit the credentials (user_uuid:secret_pin) in basic auth format encrypted with Algorithm: AES/CBC/PKCS5Padding with key We4c4HYS5eagYdshfEP2KY27KwkjaZNH
However it was found that the same api can be accessed with removing the is_encrypted: 1 flag and then submitting the credentials in basic auth format (user_uuid:secret_pin)
Attack path
- Use vulnerability #2 to set and takeover pin of any user
- Call the api directly as described above to access function or data directly
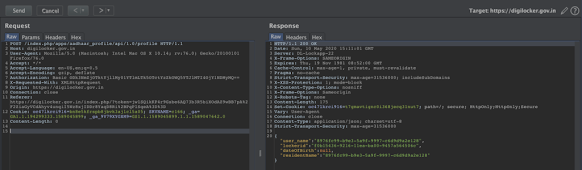
Sample call from mobile app
Sample call removing the header flag and using unencrypted credentials
Output of Custom script to monitor crypto functions in the mobile app
4) Weak SSL pinning mechanism in mobile app – Medium
The app uses weak ssl pinning it can be bypass easily with tools like Frida and known techniques.




This comment has been removed by the author.
ReplyDeleteUnlocking the digital treasure was a journey, and I couldn't have done it without the right tools. Just as a treasure map guides you, expertly crafted Online assignment writing services .were my compass in the academic maze. They provided me with the insights and support needed to navigate and succeed.
ReplyDelete
ReplyDeleteCaring for your motorcycle helmet includes cleaning, proper storage, and adhering to the manufacturer's instructions. Regular inspections are vital, and you should replace your helmet every five years or after accidents. Look at this web-site Helmet Price in Bangladesh.
I am pleased to have come across this subject, but I do not have any detailed information about it at the moment. I would like to mention an important point regarding OTHM Assignment Writers UK, I also discuss assignments and the difficulties students encounter when they do not have a sufficient understanding of their assignments and dissertations.
ReplyDeletepg game slot pocket games ได้ก้าวขึ้นมาเป็นหนึ่งในนวัตกรรมที่น่าติดตามในโลกของเกมสล็อตออนไลน์ pg slot เกมนี้ไม่เพียงทำให้ผู้เล่นตื่นเต้นและสนุกสนาน กราฟิกที่ทันสมัยและความคล่องตัว
ReplyDeleteNice Blog
ReplyDeleteTESTING TOOLS ONLINE TRAINING IN HYDERABAD
TESTING TOOLS ONLINE TRAINING IN HYDERABAD
I have learned alot of things in this blog. This is really helpful and informative for me.If you are looking to buy the best online obu thesis service turnout to the thesis writing help for all the academic task.
ReplyDeleteWow, your content is incredibly insightful and well-written!
ReplyDeleteIt's always refreshing to see such high-quality information being shared. If you're interested,
If you're interested, feel free to check out my webpage for more related content and resources.
semi truck repair fort worth
Whoa, this is amazing! It is a tremendous accomplishment to be able to access such important data via Digilocker. In addition, I lately came upon first-rate rhinoplasty Dubai services—truly life-changing!
ReplyDeletePrepare to ace the https://www.examstrust.com/product-detail/c_stc_2405-cert-exam.html exam with confidence! This certification validates your expertise in SAP S/4HANA Cloud – Service. It covers essential topics such as service management, configuration, and integration. Whether you're an SAP consultant or aiming to boost your career, this exam showcases your skills in implementing cloud-based service solutions. Stay ahead in the SAP ecosystem by mastering the latest tools and best practices. Start your journey to certification success today and unlock new professional opportunities!
ReplyDeleteMore wellness seekers trust holistic therapy in bangalore for its authentic blend of practices like meditation, yoga, Ayurveda, and energy healing methods.
ReplyDeleteVery useful post, ideal for students searching for quality software training.
ReplyDeletedevops best institute in hyderabad
Insightful read! This highlights how powerful India’s digital public infrastructure has become and the importance of understanding secure, compliant access to platforms like DigiLocker. Knowledge-sharing like this really helps professionals and learners stay ahead in the digital era. Continuous upskilling through initiatives such as PORTAGE online classes makes navigating large-scale digital systems even more impactful.
ReplyDeleteGreat post! Re-post How I Managed to Gain Access ka experience kaafi insightful laga. Aise detailed breakdowns bohot logon ke liye helpful hotay hain, especially students ke liye jo academic pressure face karte hain. Agar kisi ko professional assignment help services In Glasgow chahiye hon, to UK Assignment Help jaisi services real support provide karti hain. Thanks for sharing this valuable content.
ReplyDeleteThis comment has been removed by the author.
ReplyDeleteWow, this is such an insightful post! Your strategies for gaining access are really impressive. I was particularly intrigued because I’ve been looking for ways to manage my workload more efficiently. For anyone struggling with tough courses, I highly recommend checking out Take My Online Class they can take my algebra class for me, which has been a total game-changer for students like me trying to stay on top of everything. Keep up the great work.
ReplyDeleteThat story about reaching India’s massive Digilocker archive is fascinating and a bit alarming. It really shows how powerful digital systems are, just like researching marketing research paper topics today globally.
ReplyDeleteWild story about unlocking Digilocker’s massive data vault—shows how digital systems can surprise us. Makes me think how smart research links with Best assignment helper when handling complex documents today.
ReplyDeleteThat Digilocker access story is eye-opening and shows how fragile digital trust can be. Reading this made me rethink like Do my online exam for me for me and focus on integrity.
ReplyDeleteHello, I’m Muhammad, I’m from Pakistan, and I am a dedicated content specialist working at Dealsexpress. I have extensive experience in writing and research within industries such as best shoes brands in Pakistan, lifestyle, and fashion. My work focuses on delivering well-structured, informative, and engaging content that helps readers make confident purchasing decisions. With a strong understanding of market trends and consumer behavior, I aim to create valuable insights that connect brands with their target audience.
ReplyDeleteIf you're searching for
ReplyDeleteorthodontics near me finding a trusted local clinic can make all the difference in achieving a confident, healthy smile. Professional orthodontic treatments like braces and clear aligners help correct misaligned teeth and bite issues effectively. A nearby orthodontist ensures convenient appointments and personalized care tailored to your needs. Modern technology now makes treatments more comfortable and discreet than ever before. Book a consultation today and take the first step toward a straighter, brighter smile.
A really useful and engaging article.
ReplyDeleteThe explanation and examples make the topic much easier to understand.
best institute for python in hyderabad join with us for Python training.
This is a very interesting analysis, and it highlights how important proper security implementation is for applications that handle sensitive user data. Discussions like these are valuable because they show how real-world testing can reveal gaps that may not be obvious during development. With government and enterprise platforms, strong encryption, secure communication, and proper validation checks should always be a priority. In the same way, organizations that rely on Microsoft power platform services also need to ensure that security, compliance, and data protection are built into the system from the start, rather than added later. Insights like yours help raise awareness about why secure design practices are essential.
ReplyDeleteThis is an intriguing and somewhat disturbing story, given all the private data contained in the various platforms today. And it makes me think, much like when buying a faux leather jacket, I need to find the perfect balance of style and protection, since our trust in someone is based upon how they responsibly manage our information and implement safety features for all users.
ReplyDelete